
Welcome to 2toLead's March 2026 Cloud Modernization Newsletter.
Cloud modernization isn't slowing down, it's accelerating, and so are the risks that come with it. This month, we're covering what's happening at the intersection of AI-assisted operations, application delivery, and security governance: from autonomous self-healing in Azure to how Copilot is reshaping your compliance posture whether you're ready or not.
If you're modernizing your cloud estate, migrating workloads, or trying to keep AI adoption from outpacing your guardrails, this edition has something for you. Let's get into it.

Thursday, April 9, 2026 | 11AM EST | Live Webinar + Q&A
Register Now to Secure Your Spot
Copilot doesn't create oversharing, it exposes it. If your organization has mis-permissioned content (and most do), Copilot will surface it fast. Join Kanwal Khipple (CEO, 2toLead) and Alpesh Nakar (CTO, EDUC4TE) as they show you how to apply Microsoft Purview controls that reduce your oversharing risk without slowing your team to a halt, even if you haven't completed your migration yet. Walk away knowing how to:
🎤 Bring your burning questions for the live Q&A.

Modern cloud estates don’t fail in clean, single-service ways. Incidents emerge from messy dependencies, and humans burn cycles stitching together logs, metrics, and “what changed.” This walkthrough frames Azure SRE Agent as a practical step toward governed, AI-assisted ops, helping teams move faster on root cause and remediation while keeping approvals and guardrails in the loop.
If your modernization program is growing, chances are your pipelines are quietly multiplying too, and that “pipeline sprawl” becomes a reliability risk long before it becomes an annoyance. This blog makes a strong case for treating CI/CD like shared infrastructure (centralized, versioned, reusable) and then pushes the conversation further: as teams start shipping AI agents, delivery needs to govern behavior, not just compile code.
If you’re modernizing VMware, you already know the pain: one upstream control-plane issue can explode into a confusing storm of alarms, and manual triage often stretches outages. This article digs into a closed-loop “autonomous self-healing” approach for AVS that correlates signals with a live dependency graph and executes policy-gated recovery aiming for bounded, verifiable restoration instead of best-effort firefighting.
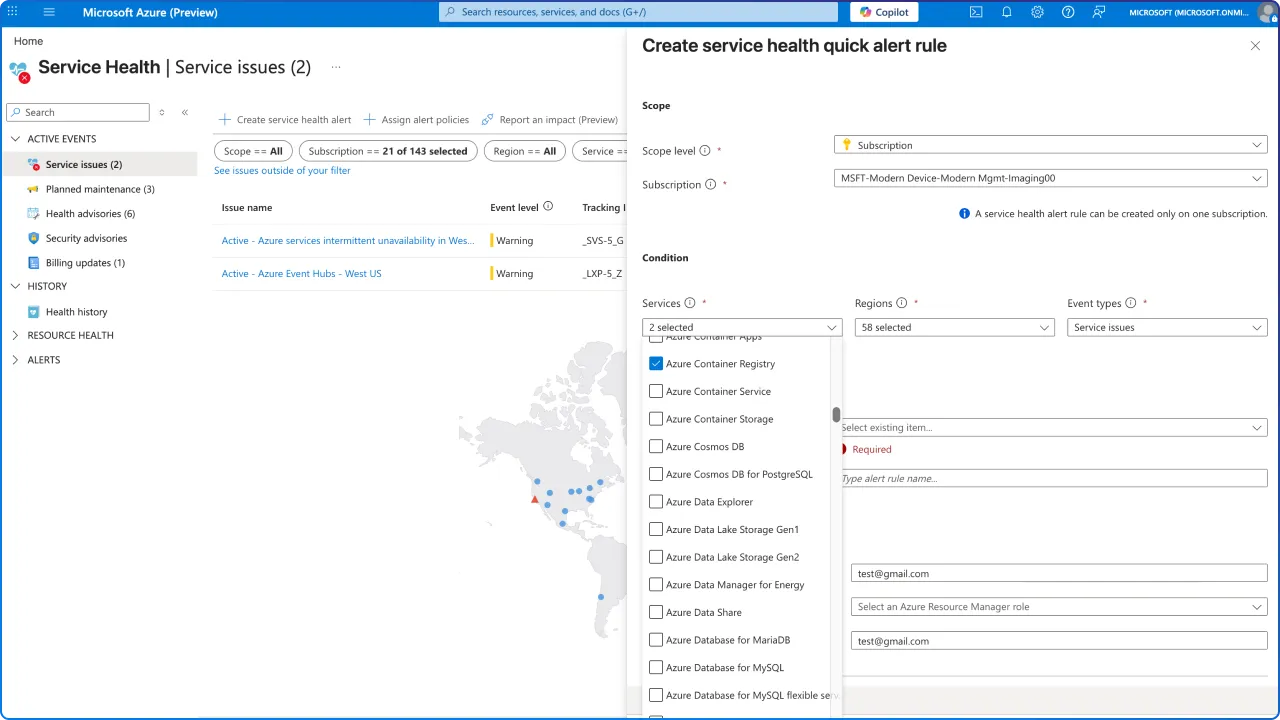
Microsoft is improving Azure Container Registry (ACR) resilience with SLI-based outage auto-detection and automated Azure Service Health alerts for critical operations like auth, image push, and pull. For DevOps and SRE teams, this means faster, clearer visibility into registry health events (affected regions/resources and mitigation context) to reduce surprises across CI/CD pipelines and container deployment workflows.
This real-world experiment shows how multi-agent AI coding can accelerate app work, when it’s engineered right, using Azure Durable Task Scheduler to orchestrate parallel tasks and Microsoft Agent Framework agents running in isolated containers on AKS/Azure Container Apps. The key takeaway for modern engineering teams: reliability comes from contracts, validation, and guardrails (not just bigger models), especially to prevent “phantom work,” broken merges, and rework in agentic development workflows.
Ingress NGINX is on a retirement timeline (upstream maintenance ending March 2026, with AKS add-on critical security patches through November 2026), so this blog outlines a practical path to modernizing AKS ingress with Azure Application Gateway for Containers (AGC). It explains AGC’s Azure-managed Layer 7 approach (including WAF support) and highlights Microsoft’s AGC Migration Utility to convert Ingress configs into Gateway API (Gateway/HTTPRoute) resources while flagging what needs manual remediation.
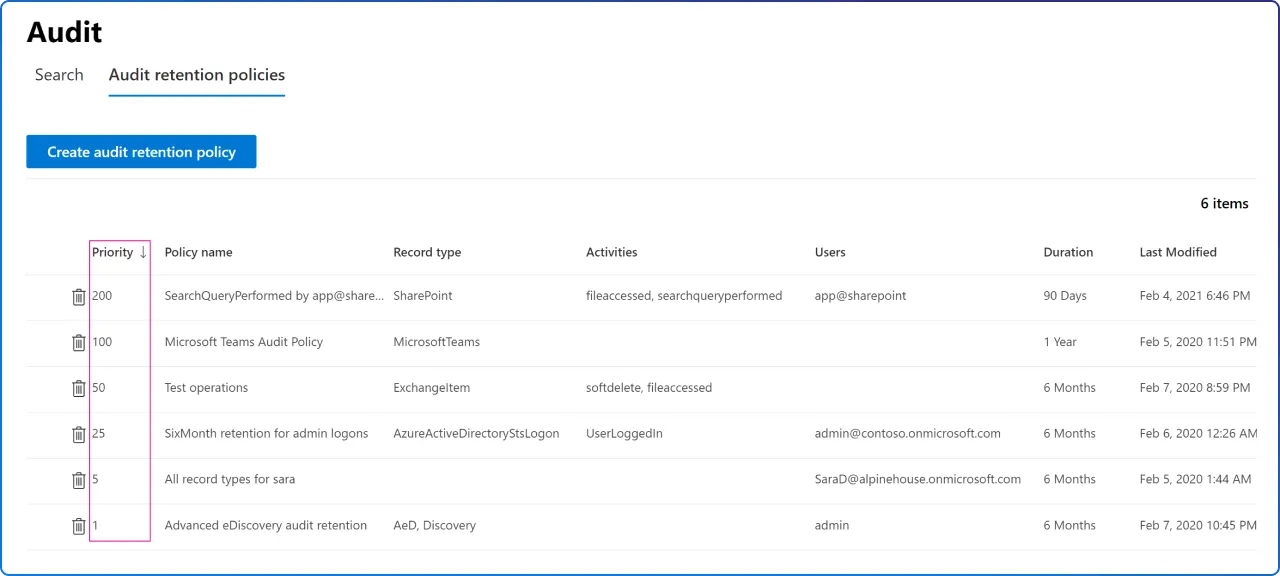
Every prompt you type, every document you summarize, and every email you draft with Copilot creates a compliance record. And through Microsoft Purview eDiscovery, admins can reconstruct a meaningful record of Copilot usage, including when interactions happened and what organizational resources were involved. Without strong governance, Copilot can amplify existing problems rather than solve them. Learn how to protect your organization before it's too late.
AI workloads can turn “normal” Kubernetes behavior into a fast path for credential theft, sometimes in under two minutes, without a CVE or container escape. Discover how routine signals (runtime installs, IMDS calls, workload identity usage) can mask attacker movement, and why cloud security teams need targeted detections for AKS/AI supply-chain risk as AI modernizes the stack.
This supply-chain case study shows how attackers abused a trusted software download channel to deliver a trojanized MSI only to public visitors, while admins saw legitimate installs. It breaks down msiexec → PowerShell execution, stealthy in-memory behavior, and browser credential/session token theft, reinforcing why governance teams must treat installer trust, telemetry, and token hygiene as core security controls.
The throughline this month is clear: modernization moves fast, but trust takes longer to build.
Whether it's AI agents operating inside your codebase, Copilot surfacing content you didn't know was exposed, or attackers exploiting the very software your team trusts, the organizations that come out ahead aren't just adopting new tools. They're building the governance, guardrails, and visibility to back them up. At 2toLead, that's exactly what we help you do.
And before you go, don't miss our upcoming webinar: Copilot-Ready Governance: Reduce Oversharing Risk with Purview Controls on Thursday, April 9 at 11AM EST. Kanwal and Alpesh will walk you through practical, actionable controls you can implement right away. Don't forget to save your spot!
Until next month. Stay sharp, stay governed.
Join Our Newsletter