
When a security incident hits, the difference between a quick, well-documented recovery and weeks of costly disruption often comes down to one capability: forensic readiness. The ability to collect, preserve, and analyze digital evidence from your cloud environment on demand.
Organizations that make forensic readiness a baseline capability shorten investigation time, reduce legal and compliance risk, and materially cut breach costs.
This article delivers a practical, playbook you can implement in Azure today: definitions and rationale, an actionable security-baseline checklist tied to Azure services, enforcement patterns at scale, retention & cost tradeoffs, chain-of-custody best practices, incident playbooks, and downloadable assets to turn advice into enforcement.
Forensic readiness is an organizational capability defined by established frameworks (notably NIST SP 800-86) that prepares people, processes, and technology to collect, preserve, and analyze digital evidence when incidents occur.
It covers what to collect, how to collect it so it’s admissible and untampered, where to store it, and how long to retain it. Implemented correctly, it reduces investigation time and strengthens legal defensibility.
Why act now? Recent industry reporting shows breach costs and recovery times remain high.
Delaying or missing critical telemetry increases detection and containment time, which in turn raises total breach cost and business disruption.
Making diagnostic logging, immutable preservation, and centralized correlation part of your baseline is a cost-effective way to reduce those risks.
Azure provides capabilities (platform logs, diagnostic settings, snapshots, immutable blob storage, and SIEM tools such as Microsoft Sentinel).
But you are responsible for configuring, retaining, protecting, and proving the integrity of evidence for your subscriptions and workloads. Treat provider features as building blocks: enable, centralize, protect, and document them to satisfy both operational and legal needs.
Below is a prioritized baseline you can implement immediately. Each item links to the Azure feature you’ll need to configure and enforce.
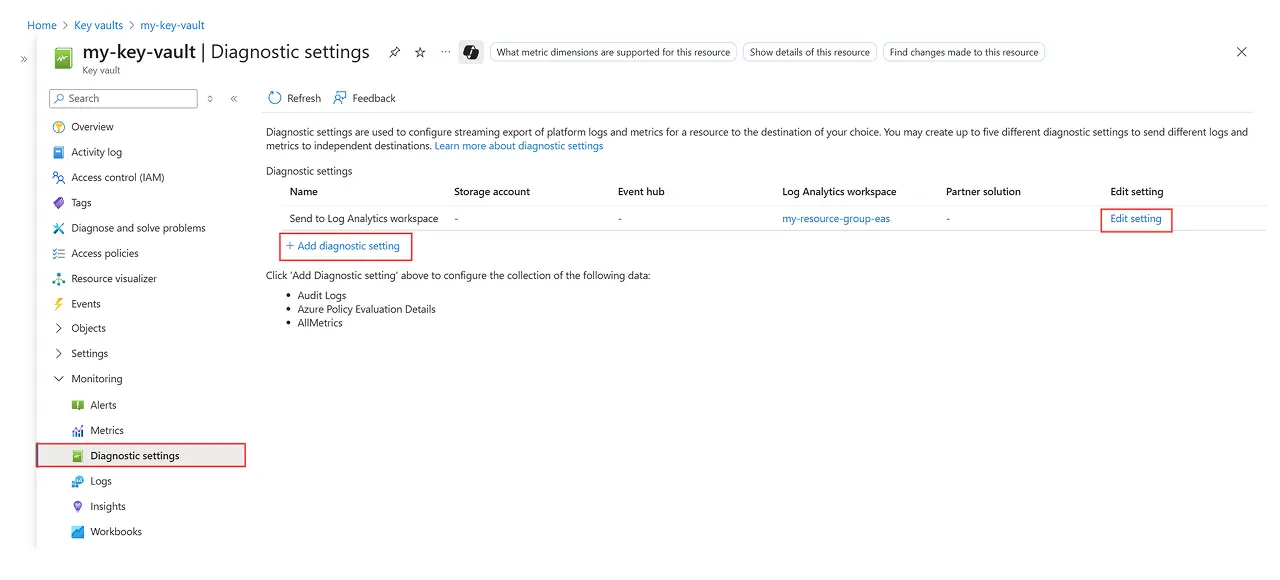
1. Enable diagnostic settings for all supported resources: Collect resource logs, metrics, and the activity log and forward them to a Log Analytics workspace, Event Hub, or Storage account. Create a diagnostic setting per resource type to capture the right log categories (e.g., AuditLogs, SigninLogs, NetworkSecurityGroupFlowEvent).
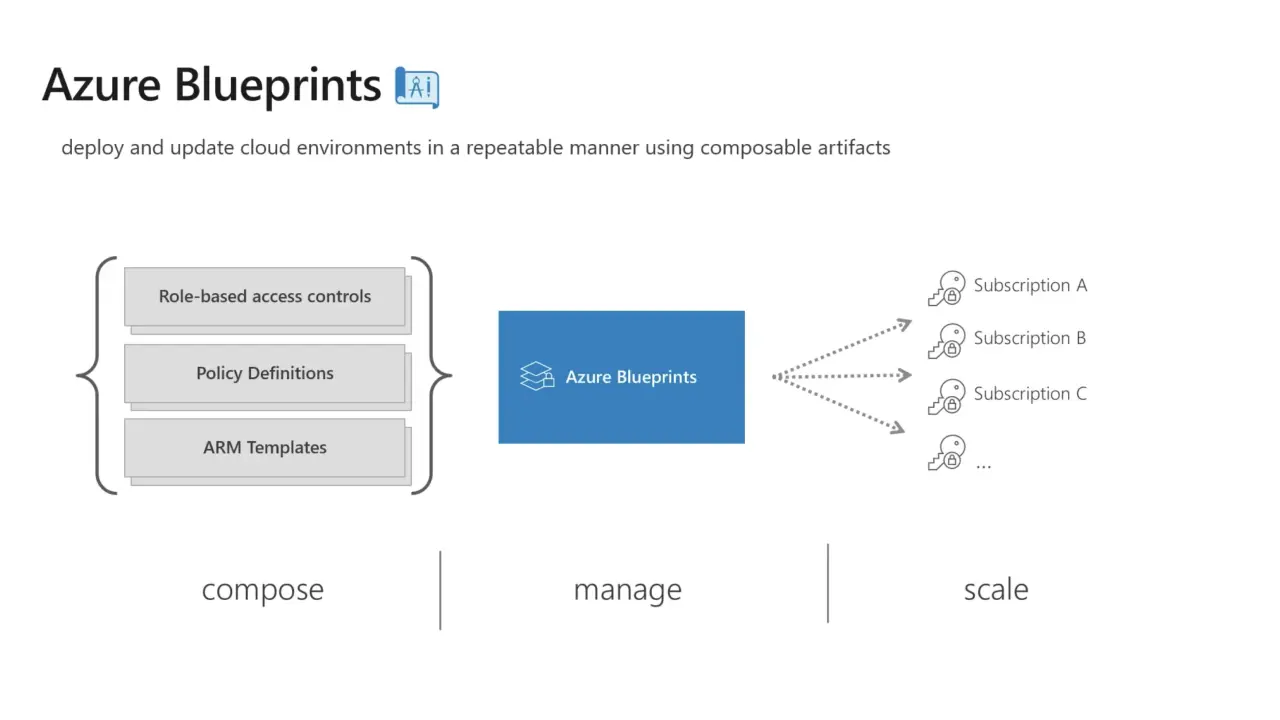
2. Enforce diagnostics at scale with Azure Policy & initiatives: Use built-in diagnostic-settings policy definitions or a DeployIfNotExists remediation to ensure new and existing resources have required diagnostics enabled. Use managed identities for remediation.
3. Centralize telemetry into a SIEM (Microsoft Sentinel): Ingest logs into Sentinel (or your preferred SIEM) for correlation, timeline building, hunting, and investigations. Use Sentinel playbooks to automate repeated evidence collection steps.
4. Automate snapshots and disk captures for suspect VMs: When a host is flagged, capture incremental or full snapshots of managed disks (and export VHDs if needed) and preserve them in a protected storage location for offline forensics. Test the snapshot → copy → export workflow in your environment.
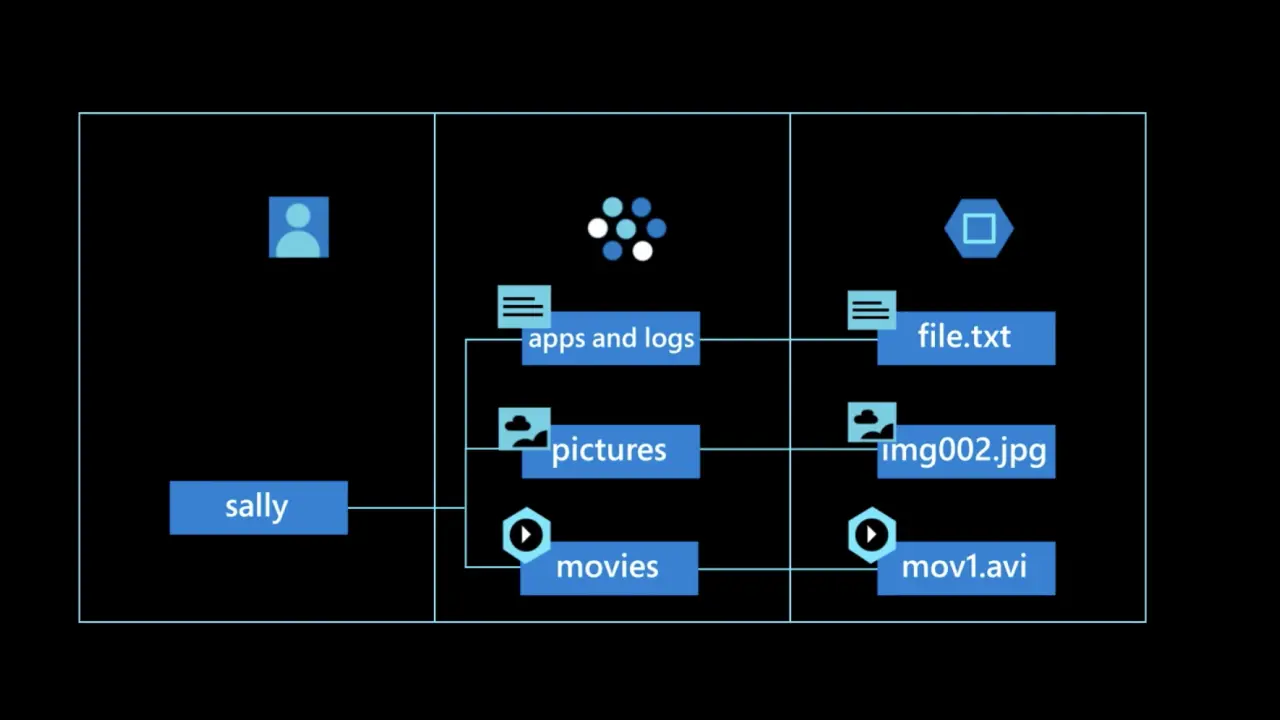
5. Use immutable storage (WORM) and legal holds for preserved evidence: Place collected artifacts (log archives, disk images, exported evidence) into Azure Blob immutable containers or enable version-level immutability and legal holds so data cannot be modified or deleted while under investigation.
6. Protect evidence and logs with strict RBAC, encryption, and Key Vault: Limit who can read/delete evidence; store keys and secrets in Key Vault with hardened access and logging; audit access to evidence stores.
7. Define retention tiers (hot/cool/archive) and retention policy by evidence type: Activity logs, security telemetry, and VM snapshots have different retention needs. Balance forensic needs against storage cost and compliance requirements (see suggested retention windows below).
8. Document chain of custody and make it automatic where possible: Record who requested evidence, when it was collected, hashes of artifacts, where it’s stored, and who accessed it. Use runbooks, Logic Apps or Sentinel playbooks to create tamper-evident audit trails.
9. Maintain a signed forensic toolkit & runbooks: Store approved scripts for volatile artifact capture, hashing, and transfer; sign them and version control them to show procedural integrity.
10. Exercise with tabletop and red-team tests: Regular exercises validate that your baseline works: you can collect, preserve, and analyze evidence within required SLAs and legal constraints.
Manual configuration is error prone. Use these enforcement patterns:
For evidence to be admissible and defensible you must show that it was collected and stored without tampering:
Azure provides a reference chain-of-custody architecture you can adapt to show auditors a defensible workflow for acquisition → preservation → analysis.
Centralization equals speed. Microsoft Sentinel can correlate disparate feeds (resource diagnostics, activity logs, Azure AD logs, Defender alerts) to build incident timelines, support hunting, and kick off automated playbooks to preserve evidence and notify stakeholders. Combine Sentinel with Defender for Cloud alerts and Purview for data discovery where necessary.
A suggested investigation flow:
Retention policy should be risk-driven, not arbitrary. Typical guidance (adjust for compliance & business needs):
Be explicit about cost tradeoffs: hot Log Analytics retention is more expensive than storing archives in blob archive tier. Use Event Hubs → cold storage → SIEM indexing only for higher-value data.
IBM and industry reporting shows that faster detection/containment reduces breach cost so weigh retention cost against the potential reduction in MTTR and impact.
Follow this checklist when an incident occurs:
Map your current posture and pick 3 priority actions from the baseline to move one level up this quarter
Forensic readiness isn’t optional. It’s a cost-saving, risk-reducing baseline. By enforcing diagnostics, automating evidence capture, and proving chain of custody in Azure, you’ll speed investigations, limit business impact, and strengthen legal defensibility.
Need help turning this into an enforceable Azure baseline? Reach out to 2toLead’s cloud security experts for a complimentary forensic-readiness review and a starter Azure Policy / ARM pack.
Join Our Newsletter